Home » IT Consultancy Northampton » Cyber Security Northampton
Your organisation’s data is critical to the operation of your business. Whether you’re starting a new business or are an established company, data is a valuable asset. It’s used to organise and run your business, communicate with customers and suppliers, as well as analyse and provide insight into every problem that a business could face. Unfortunately, other people want that data. Whether it’s to help them compete against you, attack one of your customers or suppliers, or simply prevent you from trading.
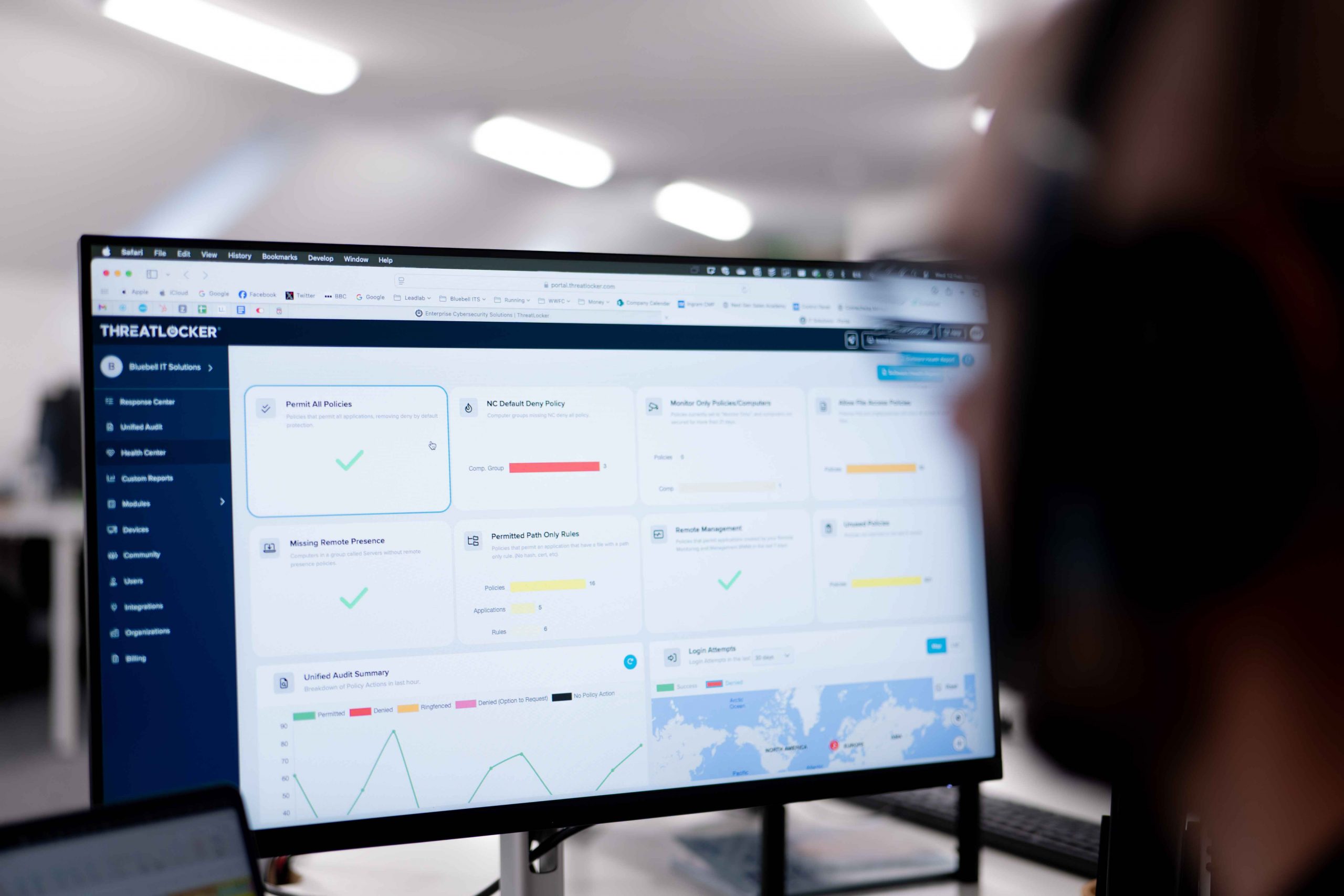
Our Cyber security Northampton Consultancy Services are delivered by trained and experienced consultants who have an understanding of the range of cyber risks facing organisations today, they will help you implement the best possible security solutions for your budget and requirements.
At Bluebell, we’re UK Government Cyber Essentials accredited and have a key focus on all our clients having the right policies and security standards in place to protect against attacks. Cyber Essentials is a government-backed, industry-supported scheme to help organisations protect themselves against common cyber-attacks. Look at getting your business accredited in Cyber Essentials in Northampton with Bluebell today.
Have an enquiry? We’re just an email or call away!
Easily identify your cyber risks with our cyber health check, which will assess your cyber risk exposure and identify a practical route to minimise your risks combining:
This service is designed for organisations that want assurances that their security measures are effective. Or potentially as a sanity check to ensure that systems installed by another provider are correct.
Our Cyber Security Audit and Review service provides an in-depth and detailed evaluation of your organisation’s cyber security posture in Northampton. This in relation to its compliance with the National Cyber Security Centre guidance. Which helps you take steps towards obtaining Cyber Essentials (or Cyber Essentials Plus) certification.
You will receive consultancy support and advice on:
This service is designed for organisations that want a high level of assurance and want to instil confidence among their customers, suppliers, and stakeholders. Any business that has Government links should also consider this service.


This risk assessment identifies, analyses, and evaluates risk. As well as ensures that the cyber security controls you choose are appropriate to the risks your organisation faces. Conducting a risk assessment can be complicated, especially as there are many different standards that could be appropriate to measure against.
We have qualified advisors in Northampton in cyber security that provide business-driven consultation on the overall process of assessing information risk. They will offer you support and guidance in the following areas:
Cyber risk assessment should be a continual activity. A comprehensive enterprise security risk assessment should be conducted at least once a year or when significant changes occur to the business, the IT estate, or legal environment to explore the risks associated with the organisation’s information systems. An enterprise security risk assessment can only give a snapshot of the risks of the information systems at a particular point in time.
A risk assessment consultancy can be performed on organisations of any size. Including small, medium-sized and large enterprises. Where the IT infrastructure includes a combination of complex legacy systems and newer operating systems whose interoperability is not always seamless.
Our team can help in developing, designing, and implementing secure architecture across IT systems. As well as networks and applications.
Our service includes consultancy, support, and guidance on the following areas:
This service is designed for existing or new businesses that are beginning to implement security controls. As well as currently implementing security and require assistance. Or those that have already implemented security controls and would like advice on ways to improve them. This service is also useful if a business has had a security breach and would like controls to be implemented.

© 2026 Bluebell IT Solutions - All rights reserved
SEO and Website Design by Loop Digital